The 17-year mystery will be broken. Who's Middleborn
The New York Times is tracking a smart mystery

Original title: My Quest to Solve Bitcoin's Great Mystery
Original by John Carreyrou with Dylan Freedman, the New York Times
Photo by Peggy Block Beats
Editor: In recent days, The New York Times published a long investigative report to re-examine a 17-year-old problem with encryption: who is China
Unlike previous speculations based on sporadic explosions or a single thread, the story follows the Cypherpunks historical archives, gradually shrunk to a key figure, Adam Back, by comparing technical pathways, writing styles and behavioral trajectories。
From Hashcash to b-money technology, to early conceptions of decentrization structures, to spelling habits and details of expression, reporting attempts to build a more systematic chain of reasoning。
The article does not give the "final answer". As noted in the text, genuine identification can only be accomplished by the signature of a private key by Chinese himself. But in the absence of direct evidence, this report offers a new approach to the issue of... - Approaching an almost unreachable puzzle through long-neglected historical material and micro detail。
At a time when Bitcoin is gradually becoming an important variable in the global financial system, the issue may well have gone beyond "who wrote the code" itself. It is more about the starting point of a technical concept: what kind of personal experience, the path of thought and the context of the times are the source of decentrization。
The following is the original text:
One evening in the fall of 2024, my wife and I were stuck on the Long Island Highway. She was tired of hearing about the jazz field that I used to play when I was driving。
That's Hard Fork, the New York Times technology program, where the moderator is discussing a new documentary from HBO claiming that Bitcoin's anonymous inventor has uncovered the true identity of his son。
I was immediately attracted. I've always thought that "Who is the middle man?" is one of the most fascinating puzzles of this time, and that it has tried to explore, but has never worked. Two years ago, I even spent a few months studying a related book, but I quickly realized that I had limited capacity and had to give up。
Now I hear that someone may have finally found this mysterious figure — a man who, with amazing genius, reshaped the financial system, created an industry of 2.4 trillion dollars and created one of the world’s greatest wealth in a moment — and I cannot help but have a feeling of admiration and jealousy. I can't wait to see this documentary. As soon as I got home that night, I log in HBO Max, click the play button。
In the end, I don't think the conclusion of "Money Electric: The Bitcoin Mystery" is convincing: HBO points a Canadian software developer to Central. But in this documentary, which is an all-too-fun, fast-truck, encrypted world, there's one piece that really bothers me。
Adam Back, a British passwordist and key player in the Bitcoin movement, sits on a park bench in Riga, Latvia, with a shirt open under a brown coat. The director refers to the names of some of the "scientific candidates". When speaking of himself, Back became obviously nervous, strongly denied that he was Chinese and asked that this dialogue not be recorded。
And We have seen how many liars, and how many of them have found small signs that identify them. Back's act -- the way he looked, the way he looked, the way he looked at him, the way he looked at him, the way he looked. I watched this on TV several times as the tails rolled。

In February 2024, British password scientist Adam Back in Miami. (Photo by The New York Times: Amir Hamja)
In thinking about Back's response, I suddenly thought of another thing: that an Australian impostor was prosecuted for lying about himself as Chinese. What if the evidence disclosed in the case in London a few months ago could help me solve this mystery
Anyone familiar with Bitcoin's "fiction" will tell you that Chung-Bun has almost done a great deal in online anonymity — with almost no digital trace left。
But he did leave a complete set of texts: a nine-page white paper that the system described his invention; and his large number of posts at the Bitcointalk Forum-- It's an online community where users discuss bitcoin software, economic models and ideas. In the course of the civil proceedings against the impostor, this library was unexpectedly expanded: Finnish programmer Martti Malmi, a leading figure in Bitcoin's early collaboration with Chung, published hundreds of his correspondence with Chung. Previously, there had also been mail from Chinese and other early Bitcoin participants, but this disclosure was far less numerous than Malmi. If China's wise will be identified one day, I believe the answer must be hidden in these texts。
But in retrospect, I'm afraid this road has already been crossed. During the past 16 years, journalists, academics and numerous web detectives have tried to reveal their own identity. During this period, more than 100 names have been put forward: from an Irish cipher student to an unemployed Japanese American engineer, to a South African criminal leader and even the mathematician prototype depicted in the film A Beautiful Mind。
The most attractive theories are often based on certain "coincidences." They coincide with the limited perception of middle-aged minds: specific programming styles, mythical work history, deep understanding of the key technologies of the Bitcoin, and some anti-government worldview. However, these assumptions eventually collapsed in the face of an alibi or other contradictory evidence. Each failure, on the other hand, makes a lot of people in the Bitcoin community happy. As they have often said, only by transferring the bitcoin in their own possession can China prove identity; until then, all the evidence can only be deduced indirectly。
It is rational to think that you can solve a puzzle that has plagued people for many years, and there is a lack of capacity. But I yearn for the excitement of chasing big, complex stories. So I decided to try again to unmask the mystery of the bitcoin founder。
Threads
Two weak breakthroughs
I first tried to find a way to narrow it down。
In the Chinese e-mail to Martti Malmi and his other texts, there is an extraordinary feature: the English spelling and expression are mixed in his language, while American usage is mixed. Given that many of the "scientific candidates" are American, there are speculations that he is deliberately using English expression to disguise his style. But I never agreed with that statement, because Nakamoto left a key clue。
In Bitcoin's first block (the Genesis block), he embedded a newspaper title: "The Times 03/Jan/2009 Chancellor on link of second bailout for banks." This makes me more inclined to think that it is likely that the Chinese are indeed from the United Kingdom。
In addition, it is highly probable that Chinese can be a member of the "Cypherpunks" (CypherPunk). This is a loose group formed in the early 1990s, with anarchism, and they want to free individuals from government surveillance and censorship by using encryption — that is, technology that protects communications through code。
The password punks communicate mainly through a "mail list". As a precursor to today's forum, mailing lists are essentially a group mail system, with subscribers receiving large text in typewriter fonts in their mailboxes and continuing the discussion through "all responses"。
It is hard to imagine that one of the core concerns of the year was the digitization of financial transactions in a time when Venmo and Apple Pay had become universal. When you hand someone a 20-dollar note, nobody knows where the money comes from; but once you pay with a check or a credit card, the bank leaves an electronic record. Password punk fears that the Government may use these records to track personal life. Thus, in their mailing lists, there is a constant search for the creation of "electronic cash" — a digital currency that preserves the anonymity of cash. Some have even introduced their own electronic cash programmes, but they have not been universal — until Bitcoin appears。
In addition to the consistency of the concept of "electronic cash", there are other indications that Chinese and Chinese minds belong to this group: he published his own white paper on one of the branches of the code punk mailing list, the "Cryptography" list, and seemed familiar with two members of the group。
However, even in the late 1990s, there were about 2,000 followers of code punks, which still means a rather large pool of candidates。
With these not very powerful clues, I began to read all the texts left behind in Chinese, especially the e-mails published by Martti Malmi, and to sort out a list of words and expressions that, in my opinion, are "unusual." It's like breaking a strange dialect. On several occasions, I even wondered if I was just doing a futile thing。
my list eventually extends to more than a hundred words and phrases, which occupy several pages of the notebook. some of them are of particular interest to me: "dang" "backup" (used as a verb, synthesis of a word), "human friendly" "on penciple" "burning the money" "hand tuned" and "partial pre-image"。
there's one sentence -- "a woman to the network" -- – sounds like a line in a science-fiction movie; the rest of the expression reveals a strange mixture: both a british upper class and an american country accent, and a combination of computer hackers and password scientists’ language habits。
Using the advanced search function of social platform X, I performed a cursory screening to see if the people most often suspected of being mid-middle-middle-heart had used the words I had marked. Not all "candidatures" have X accounts, so it's not a strict method. But, as I expected, one of them has a high degree of overlap with my vocabulary list — Adam Back。
When I looked at a long list of ticks under his name in the notebook, an adrenaline surged. My instinct seems to have at least some basis. Back may not be able to convince a community that has been studying this issue for many years, but I can hardly believe it is a coincidence。
When I looked further at Back, I found out that he did have a number of characteristics that matched the Chinese. First of all, he is British and is a member of the "Cypherpunks". More crucially, he invented Hashcash — a system based on probabilistic calculation of difficult issues, and it was the mechanism that was used by the Chinese delegation to achieve the "mining" of Bitcoin. In the Bitcoin White Paper, Chung clearly quoted Back and his Hashcash work。
However, at the hearing of the Australian impostor, Adam Back submitted a set of e-mails indicating that he had been contacted by China in August 2008 prior to the issuance of the Bitcoin White Paper to verify the presentation of his Hashcash paper. These e-mails seem to almost prove that Back can't be mid-heart。
But then again, I think, I see another possibility: these emails, too, may be a cover-up by Back to cover themselves。
The rabbit hole that crashed into the code
With thin glasses, thinner gray hair and goatee, 55-year-old Adam Back looks like a slightly smug mathematician. Over the past 10 years, he has built a “small business map” around bitcoin and has become one of the most influential figures in this community。
Back has long been one of the most popular candidates among the "scientific" candidates. However, unlike some of the other main suspects, he was not subjected to in-depth media research — with the exception of a video released in 2020 by an anonymous YouTube (the online name “Barely Sociable”)。
A year ago, I flew to Vegas to meet him. He was invited to speak at the Bitcoin 2025 conference at the Venice Resort. I wasn't sure I had the right person, so I didn't intend to confront him immediately. I just want to know him first and know more about his background. If the follow-up investigation can hold, I envisage, at some point, putting all the evidence in front of him for a "final confrontation" similar to the one the detectives forced on the suspect. But right now, I would rather let him relax and establish a basic relationship of trust。
I spoke to him before a forum ended. On the stage, he confidently predicted that the price would be about $108,000 bitcoin and that it would rise to $1 million over the next five to ten years. (The stage of his speech was named Nakamoto Stage by the host.) Although we had already arranged an interview, he was somewhat surprised to see me。

Adam Back gave a speech at Bitcoin 2025 Conference last May in Las Vegas. (Source: Bloomberg, Photo: Ronda Church)
I only told Back that I was writing a story about the history of bitcoin. But he may have sensed my real intentions. Before that, I had contacted six of the three former colleagues he had been involved in. If he had doubts, he had not shown. He has always been patient and friendly. It's hard to imagine that this medium-aged "technology house" that whispers softly and that seems unprepared may be one of the richest people in the world. According to the Bitcoin Circle, China has dug up about 1.1 million bitcoins at an early stage — an asset valued at $118 billion at the prices of the conference。
When it comes to bitcoin, Back seems rather talkative; but when I turn the subject to his early years, he gets more cautious. In the end, I put together some information from him: He was born in London in 1970, with an entrepreneur and a legal secretary. Families often move and have a clear view and do not shy away from expressing themselves。
Back mentioned that when he was 11 years old, he had been doing self-learning programming on a Timex Sinclair personal computer and had begun to become interested in cryptography in high school. This interest was gradually turned into enthusiasm when the doctorate in computer science was taught by a fellow student about PGP (a free encryption program), which was widely used by anti-nuclear activists and human rights organizations to protect documents and e-mails from government surveillance。
Back is fascinated by the potential application of the PGP. He said that he spent almost most of his time reading the book "drilling into a coded rabbit hole". The result was a severe deviation from the main line so that the paper had to be completed in the last six months, which he described as an “emergency plane like a pilot”。
AND THEN I REALIZED THAT PGP RELIED ON PUBLIC KEY CRYPTOGRAPHY. BITCOIN IS ALSO BASED ON THIS MECHANISM. A BITCOIN USER HAS TWO "KEYS": A PUBLIC KEY, WHICH GENERATES AN ADDRESS EQUIVALENT TO A DIGITAL SAFE; AND A PRIVATE KEY, WHICH SERVES AS A SECRET PASSWORD TO OPEN THE SAFE AND DISPOSE OF THE ASSETS IN IT。
I can't help but feel the meaning: Back's "interest" at the post-graduate level is exactly the same as the core code technology that was adopted later by Nakamoto。
Back also told me that his doctoral thesis was directed at distributed computing systems — software systems that operated in concert with a set of independent computers (known in computer terms as “nodes”). And this also constitutes another key technological base for bitcoin。
IN ADDITION, HIS PAPER PROJECT WAS MAINLY DONE IN THE C++ LANGUAGE, WHICH IS THE PROGRAMMING LANGUAGE USED IN THE ORIGINAL VERSION OF BITCOIN PREPARED BY CHINESE。
Almost two hours later, Back politely stated that other arrangements had been made that night, and we ended the meeting amicably. I told him to contact him if there were any questions later。
Be a "cipher punk."
Before I went to Las Vegas, I started immersing myself in the files of the Cypherpunks mailing list, trying to understand the mysterious underground world that gave birth to the wise. When I got back to New York, I stuck myself in it again。
Unlike social platforms like Facebook, Cyberpunks mailing lists are a decentrized space for communication. There, a group of private-minded cryptographic extremists gather to freely discuss subversive ideas without fear of censorship. In the process, they inadvertently planted some technological seeds that later changed the course of financial history。
These discussions were kept on unknown websites. One of the websites greeted me with a skull and crossbone symbol and wrote a slogan: "Stand up, the only thing you'll lose is the fence of the wire!" I looked at thousands of e-mails, filled with coden terminology that I could hardly fully understand。
Adam Back was added to this mailing list in the summer of 1995, when he was close to completing graduate studies. He quickly became an active and straightforward participant in it, with frequent postings, extending from digital privacy to his own rather economical habits of life。
In some of his earliest posts, Adam Back had solved a password challenge -- a task like a mathematical puzzle. The question was released by the California code punk Hal Finney, who was involved in the development of the PGP. This also marks the beginning of online friendship between the two: Several decades later, Back on social platforms, they interacted with each other inside and outside the mailing list, and he has always appreciated Finney's focus and programming skills。
Sino-sung and Finney are just as friendly. During the publication of the Bitcoin White Paper by Chung, Finnney publicly expressed his appreciation. Later, he also took the initiative to take over bitcoin, completing the first bitcoin deal in history. Although there is no evidence that Finney knew the true identity of Chinese intelligence, one interaction between them suggests that Chinese intelligence is not new to Finny。
In December 2010, Finney posted praises for bitcointalk. Then, two hours later, he replied, "It is important to have your approval, Hal."
And there's one other thing that makes me think there might be an earlier connection between Nakamoto and Finney. In an e-mail to Martti Malmi, Chen was referring to an electronic cash system designed by Finney, Reusable Proofs of Work (RPOW)。
Similar to bitcoin, RPOW also introduced the Hashcash mechanism in the design; but differently, it hardly attracted the attention of the coding community. Only a very small number of people have discussed the system in the password lists of punk and Criptography。
And one of them, just Adam Back。
A gold mine
In the group "Cypherpunks", Adam Back found a kind of one of his own. I can't help but imagine his home in London, after work, using dial-up Internet access to argue all night with members across the globe about various philosophical issues。
Like many of these pen pals, Back believes in "crypto anarchy" — a concept that advocates the isolation of personal life from State power intervention through encryption。
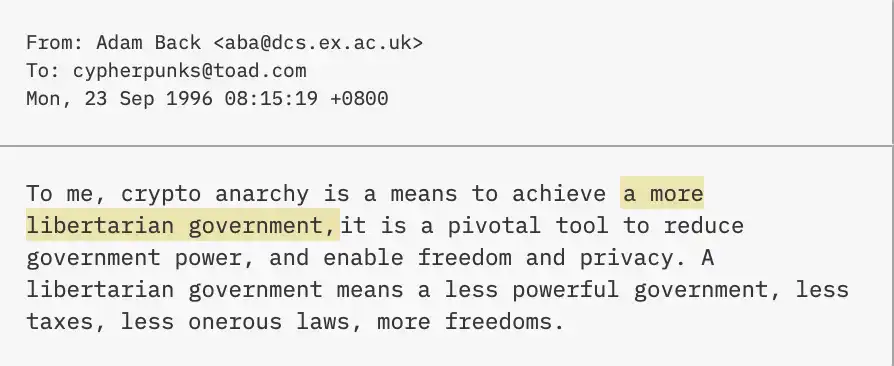
This reminds me of what Nakamoto said when he introduced Bitcoin:
As a liberal, Adam Back was outraged by the Clinton administration's criminal investigation of the founders of the PGP. At that time, the United States Government regarded encryption as an important component of national security and considered the posting of PGP source codes on the Internet as equivalent to the export of prohibited military materiel。
For this reason, Back launched a rather ironic protest: he printed an imposed algorithm on a T-shirt and sent it to members of the "Cypherpunks" in other countries. His intention was clear — the United States ban on the export of sensitive encryption technology was contrary to the principle of freedom of expression and could not be truly implemented。
While I was groaning about the charade, I suddenly realized that Chinese minds were actually sending political messages by code. It is likely that the title of The Times, embedded in the creation block, was used to express dissatisfaction with the British government’s banking rescue policy during the financial crisis。
He also left another layer of "political metaphors" on a website that goes to central technology fans: He set his birthday at 5 April 1975. And April 5, when Franklin D. Roosevelt banned private gold in 1933 in order to depreciate the dollar during the Great Depression, was the year when the ban was lifted。
Financial commentator Dominic Frisby discovered the egg more than 10 years ago and pointed out its meaning: Bitcoin was essentially a digital gold, and the State could neither prohibit nor artificially depreciate。
But nobody seems to notice that Adam Back published a short post in 2002: "It's just a little curious why the United States banned private possession of gold? It's hard to understand
A commitment to garbage information
In thinking about this strange coincidence, I also noticed another resemblance between Chung and Adam Back: They all have a near-obstinate interest in “spam”。
Among the numerous "amateur projects" during the Punk period, Back operated an anonymous relay service (remailer) that could remove identity information from it before forwarding it, thus enabling anonymous communications. However, he was very upset that the service was quickly abused by spam senders and used to send useless messages to others。
To solve this problem, Back invented Hashcash in March 1997. The core idea is to charge "post money" for every mail sent through the service. This "postage" is paid in the form of Hashcash, and users need to calculate to solve some of the small mathematical problems to obtain it. For ordinary users, these calculations take only a few seconds; but for spam senders who send hundreds of thousands of e-mails at once, this would result in significant resource costs to effectively curb abuse。
The word “spam” is almost everywhere when I read the text from the second and third reading. In rough statistics, China has mentioned at least 24 times, and many of his points of view are almost identical to Back's thinking。
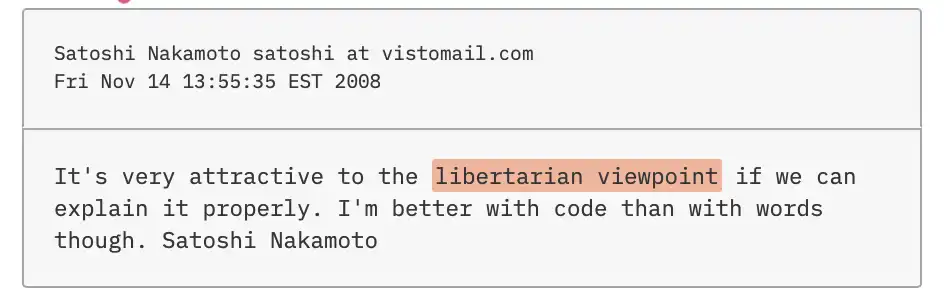
Five months after the launch of Hashcash, Back proposed on the Cypherpunks mailing list, a mechanism that might help celebrities screen their mail. And in a post published in January 2009 in the Cryptography mailing list, Sino-Hyun had similar ideas — only this time, he used bitcoin。
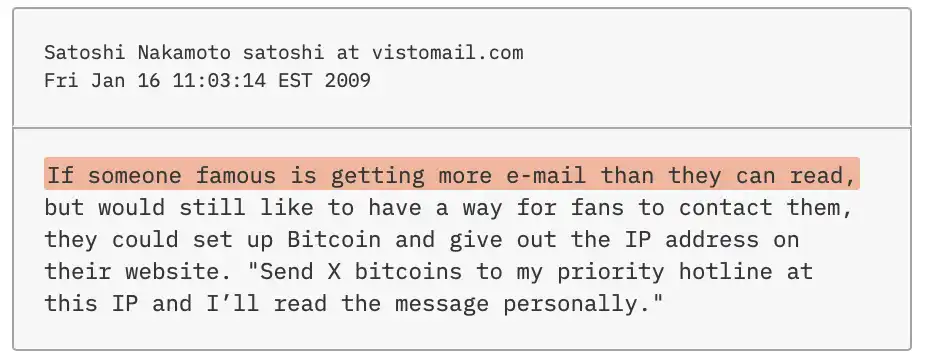
It is difficult to see this use as a natural application of the new electronic currency like Chinese -- that's what Adam Back has been thinking for over a decade。
China also believed that bitcoin might be able to reduce waste information in general. In the days following his White Paper, he suggested that the system might provide a new use for the "Zombie Computer Network" that was controlled by hackers and used to send spam to mailboxes - "to turn to the production of bitcoin"。
That view had not attracted much attention at the time, and spam was still widespread. But four years later, Back made almost identical observations on Bitcointalk: "If CPU/GPU mining based on Hashcash were more profitable than sending spam, spam might even be reduced. I think that's probably happening
Mr. Everage
IN THE SEARCH FOR THE CRACKS IN CHINA'S SMART AND SOPHISTICATED DISGUISE, I HAVE NOT BEEN ABLE TO MOVE WELL, NOR HAVE I EVER BEEN ABLE TO FIND A TRULY DECISIVE "CLARIFICATION". THE PREVAILING VIEW WAS THAT HE HAD MADE TWO MISTAKES: ONE WAS A LEAKED IP ADDRESS, WHICH SEEMED TO LOCATE HIM IN SOUTHERN CALIFORNIA AT THE TIME THE BITCOIN SOFTWARE WAS RELEASED; THE OTHER WAS THE HACKING OF ONE OF HIS MAILBOX ACCOUNTS. BUT AFTER A FEW WEEKS OF PURSUING THESE TWO LEADS, I CAME TO THE CONCLUSION THAT NOT ONLY ARE THEY FRUITLESS, BUT THEY MAY NOT EVEN BE TRUE "FAULTS" FROM THE OUTSET. WHERE ELSE COULD I HAVE DONE IT IN THE FACE OF SUCH AN ALMOST PERFECT HIDEAWAY
As I think about it, I realize that Adam Back is also very good at keeping anonymous on the Internet. He had deep mistrust of government surveillance, and almost always wondered how to circumvent it. As a matter of fact, like Nakamoto, Back is a great admirer of aliases。
In January 1998, he wrote, "You have to stay under radar, largely "invisible" for the government; the intelligence agency's file on you should only say "Mr. General" and it seems completely harmless. Then set up for you one or more doubles of your own true interest."
The "substitute" selected by Chung is from Japan. Interestingly, Back in 1997, when a Japanese member of the "Cypherpunks" discussed the creation of Japan’s first anonymous forwarding service, Back showed interest in the country。

Adam Back gave a speech in Miami in February this year. Like Chung, he has a deep understanding of cybersecurity. (Source: The New York Times, Photo: Amir Hamja)
"Congratulations on launching an anonymous referral service in a new jurisdiction!" Back then, Back said, "It's nice to have a few more jurisdictions -- I don't know what the advantage of Japan is in this. Is there anything legal in Japan that is not legal in Europe or the United States?"
The Japanese password punk didn't reply. But that doesn't prevent Back from doing some research on his own. If he did, he might find a company with a registered address in Tokyo, Anonymousspeech L.L.C., which provides anonymous mailboxes and web hosting services. It is through this company that China has registered Bitcoin.org domain names and created two untraceable mailbox accounts。
In 1999, Back moved to Montreal to join a start-up company focused on privacy software. There, he was involved in the development of a privacy system called Freedom Network, which allowed users to view the Internet anonymously. The system was later seen as a precursor to Tor, which hides network traffic through multiple layers of encryption. There is a general perception in the Bitcoin community that it's to use Tor to hide their whereabouts。
Similar to bitcoin, Freedom Network is also a distributed computing system. Back and his colleagues tried to get it to "immunize" government and business surveillance。
This is another thing he shares with Chung: his statement in Bitcointalk shows that he has a very deep understanding of cybersecurity and how to prevent loopholes. The Bitcoin network is highly appreciated in large part because of its robustness during years of hacking。
Napster vs. Gnutella
During the months of in-depth study of the "Cypherpunks" mailing list file, I sometimes lost my way into some strange dead end. For example, in response to early criticism of the White Paper in the Cryptography mailing list, he wrote, "I could actually express it a little bit stronger." I always felt that I had seen it before, and it took me several nights to look over the old post on the list in the 1990s and find it, but it was my fault。
However, this "rereading" has not yielded nothing. There are more similarities between Adam Back and Chung. For example, both have a clear negative attitude towards the copyright system. In September 1997, Back wrote:。
And it's this idea that drives him to publish his own anti-spam tool, Hashcash。
CHINA HAS TAKEN A SIMILAR APPROACH. HE ISSUED BITCOIN SOFTWARE UNDER AN MIT OPEN SOURCE LICENCE, ALLOWING FREE USE, MODIFICATION AND DISTRIBUTION TO ANYONE。
Under the concept of "Innovation in the Public Field", Back and Chung created mailing lists around their respective items — the Hashcash and Bitcoin-dev lists — in which software updates are published, listing new features and loopholes. And the format and style of these updates are strikingly similar。
“Back-type bias” against copyrights is also reflected in other ways. When he shared his own design of Bitcointalk, Logo, he expressly abandoned copyright and encouraged others to “directly place the improved design in the public domain”。
At the beginning of the 21st century, copyright enforcement became the dominant topic - The problem reached its peak when Napster was forced to close after being sued by a large record company. Napster is a point-to-peer software that allows users to share content directly with each other, thus bypassing business intermediaries。
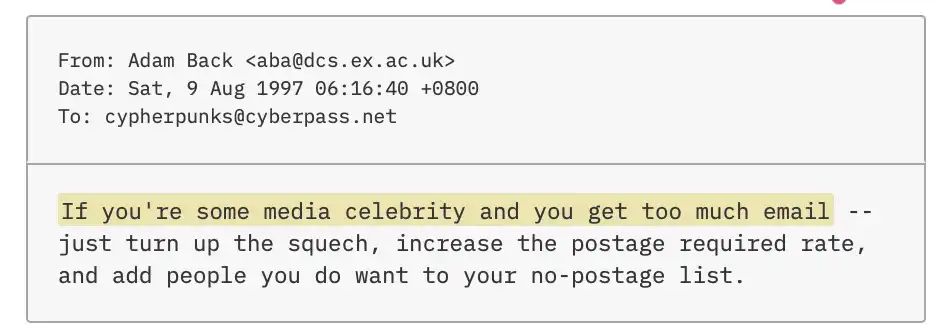
This result shocked Adam Back. He shared an article written by an intellectual property lawyer in the "Cypherpunks" mailing list, detailing the legal risks that point-to-point software developers may face. "After reading, I conclude that Back wrote, "The safest and simplest way is to distribute such software anonymously."
Bitcoin, like Napster, is essentially a point-to-point software. It's just that if the "record company" were replaced by "government", it would be quite possible to repeat the situation. Once the identity of the founder is revealed, the government lawyer will know who to blame; if the identity remains hidden, there will be no clear prosecution. If Back is really the same person as Nakamoto, it might explain his insistence on anonymity。
While record companies protect their own commercial interests, Governments have different motivations — to maintain their monopoly on currency issuance. At this point, China is like Back: they see Napster's collapse as a warning case。
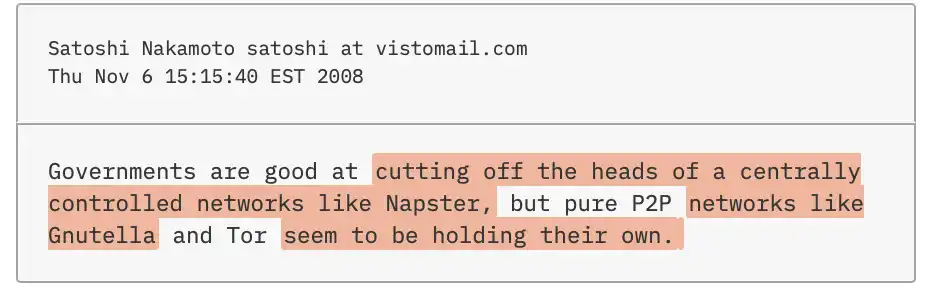
He refers to the fact that, although Napster's users exchange music files directly with each other, it still relies on a central server to record “who owns what songs”. By contrast, another file-sharing service, Gnutella, operates on a network of independent, globally dispersed computers — like the bitcoin architecture。
And this is another interesting coincidence: Adam Back made almost identical comparisons in a post in May 2000。
And, Adam Back didn't just mention it occasionally... He made the same comparison three times on the "Cypherpunks" mailing list。
Buried Road Map
Ten years before Bitcoin was born
These similarities are interesting, but I still lack the evidence to link Adam Back directly to the birth of Bitcoin. Until I found a set of posts he published on the "Cypherpunks" mailing list between 1997 and 1999, which was a whole decade ago。
On 30 April 1997, Back had proposed the construction of an electronic cash system “out of the modern banking system” and envisaged that it should have four key features: protection of the privacy of both paying parties; operation through computer network distribution in order to increase the resilience to closure; internal scarcity to prevent inflation; and non-dependence on trust to any individual or bank. Two days later, he added a fifth element: an agreement mechanism that could be validated by the public。
These five elements, without exception, became the core design principles of Bitcoin。
And four months later, Adam Back returned to the subject of electronic cash and introduced a new character based on game theory. "I've been thinking about an application to create a distributed banking system," he wrote, "Well, ideally, all nodes of the system are equivalent, and there must be k collusive in n to disrupt the system
Back is referring to the question of the famous Byzantine — a computer science problem that has long plagued the central system. In this analogy, a general who surrounds an enemy city must attack simultaneously if he is to succeed; but a general who may be a traitor would destroy the plan. Similarly, in distributed computing networks, some malicious nodes may also damage the system。
Back was conceived as an electronic cash network with a large number of nodes spread around the country, making it difficult for anyone who wanted to destroy the system to find enough "collaborators"。
This idea is almost the same as what was described in the White Paper 11 years later: the Bitcoin system can function as long as "most of the calculations are in the hands of the nodes of uncollaborated attacks."。
In the Cypherpunks post in 1997, Back mentioned nodes that could "go and go" without affecting the system, while in the White Paper, the middleman wrote that nodes could "go out and re-enter the network at any time"。
The formulation is slightly different, but it does not need to be seen by top cipherists that the two proposed the same mechanism in essence。
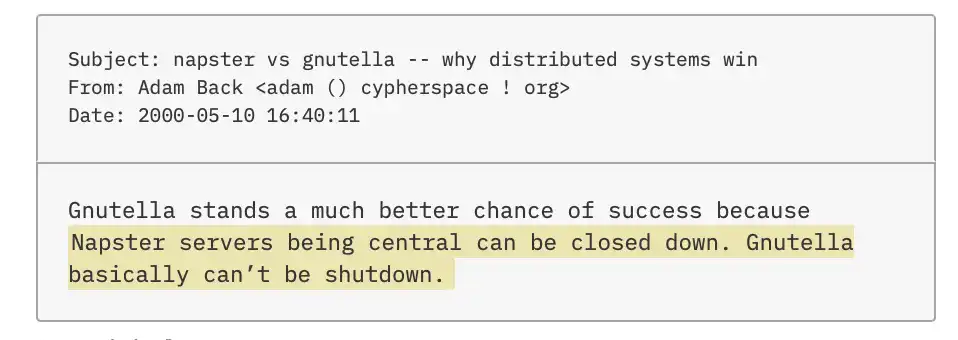
On December 6, 1998, Back again discussed electronic cash, this time after another code punk Wei Dai presented his vision — b-money. As YouTube 'Barely Social' points out in a 2020 video, Back quickly seized the proposal。
b-money uses public key passwords to keep accounts anonymous, thereby protecting the privacy of both paying parties, as previously envisaged by Back. Besides, it's got another type of Back that really appreciates。
Anyone who tries to design a digital currency faces a problem: how to issue a new currency. Wei Dai proposes a mechanism whereby newly generated b-money can be rewarded by users who solve computational difficulties。

Adam Back spoke at a seminar in Tokyo in 2019. (Source: Kiyoshi Ota/Pool)
Back invented Hashcash is very similar to the mechanism: It trades for "authorities" to send mail by allowing users to solve computational difficulties. He further suggested that Hashcash could be used as a mechanism for issuing the electronic currency proposed by Wei Dai。
This is particularly critical, as China has quoted Wei Dai in the White Paper and later clearly described Bitcoin as a "realization of the b-money proposal"。
When I stopped to think about it, this resemblance was almost chilling: as Back envisaged in 1998, China had created bitcoin by combining the concepts of Hashcash and b-money. What is the probability of such overlap
And that's not all. In a December 1998 comment on b-money, Back even anticipated a solution that was later used to solve inflation problems。
Any electronic currency issued through "computing the dilemma" will face a problem: As the chips increase in their calculus, the problem becomes easier to solve and the speed of currency issuance increases, leading to uncontrolled inflation. In order to address this problem, Back suggested that the difficulty of calculating for the issuance of each b-money should be "increasing over time"。
This is precisely the design that was adopted in Bitcoin: he set the average generation time for each new block at 10 minutes and adjusted it by algorithms dynamically making it difficult to solve problems automatically when computing capacity increases and block speeds accelerate, to maintain the stable rhythm of the system。
As if these "predict" insights were not enough, Adam Back introduced another key concept in April 1999: To make the distributed electronic cash system truly operational, it is necessary to provide an open, unmistakable time stamp for each transaction. Otherwise, the same currency could be duplicated, thus placing the entire system in disarray。
Back's solution is to use Hash trees — a structure that can compress large amounts of data into a single “digital fingerprint” — and publish them in the New York Times classified ad。
In Bitcoin, China has adopted the same approach, except for replacing the "press announcement" with the Hashcash mechanism: by means of high-intensity calculations, wrapping transactions into blocks, creating a time stamp -- Since the falsification of such calculations is extremely expensive in terms of cost and time, it is difficult to tamper with this time record。
Even one of the most frequently criticized later on in Bitcoin — the issue of high energy consumption — Back had been prejudiced。
In 1998 and 1999, he suggested that the energy consumed by the combination of Hashcash and the electronic cash system was likely to remain below the overall energy consumption of the traditional banking system. Ten years later, when an early reader was reading the Bitcoin White Paper, he made a similar question, and the response was almost the same as that of Back。
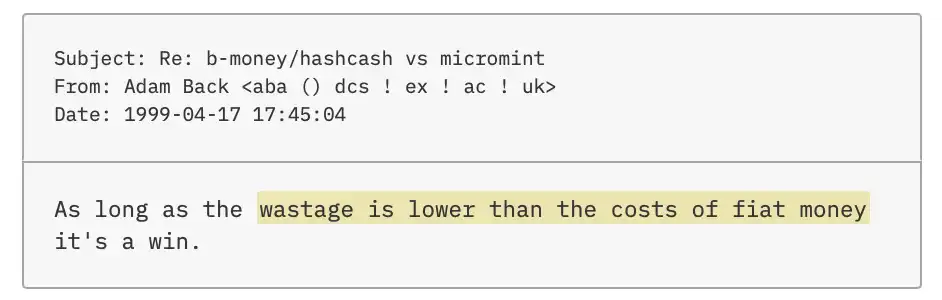
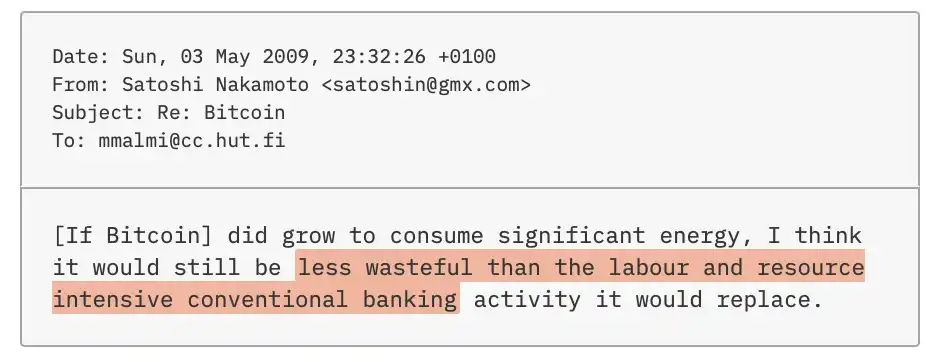
In short, Adam Back, almost 10 years before Bitcoin was born, had conceived most of its core elements — even the logic of justifying its greatest controversy (high energy consumption) — as was the case with Chinese。
Radio silence
A month after my meeting in Las Vegas, I sent Back an e-mail asking about his career and why he moved to Malta in 2009. I do not explain the motives for asking questions, but it has been pointed out in the Bitcoin community that this "tax haven" in Europe is an ideal place of residence for the middle-born, who holds a large amount of bitcoin。
The next day, Back responded to the e-mail — politely, but clearly understood the meaning behind my question. He wrote that there were many reasons for moving to Malta, including the cost of living, the climate, and, yes, taxes. "The people in the Bitcoin Circle love to be detectives, but coincidence does exist, and it doesn't necessarily mean anything."
He obviously knows what I'm trying to do. It's time to try one more step forward and ask the question that's been bothering me。
In the White Paper, Chung quoted both Hashcash and Wei Dai b-money. However, during the hearing of the Australian impostor Craig Wright, the mail submitted by Adam Back showed that Ben had contacted him in mid-August 2008 to verify the citation of the Hashcash paper and that he did not seem to know the existence of b-money. The e-mail suggests that only after Back led him to Wei Dai's site did he add b-money to the White Paper。
But that does not seem to me to be true. The Back Hashcash paper itself explicitly mentions b-money as one of its potential applications. Since he intends to quote the paper, it is logical that he must have read it, and he cannot be unaware of b-money。
Back himself admitted this contradiction in 2020. When he proposed on X that Chinese Chung might be an anonymous password punk, users questioned the idea that the anonymous sender had mentioned b-money long ago, while Chinese Chung had "know" from Back years later。
Back responded, "It's true, but Chinese deaf may be hiding from me, pretending he doesn't know b-money." He further explained, "If he knew some very cold quotations (such as the pages mentioned when discussing electronic cash in the password punk mailing list), he might not be able to quote directly to avoid being identified through these clues

Adam Back in Miami. (Source: The New York Times, Photo: Amir Hamja)
People like Back — the only six users on the Cypherpunks and Crystal mailing lists who have explicitly discussed b-money and mentioned it as many as 60 times — are particularly motivated to avoid this “reverse position”。
The more I think about it, the more suspicious it is: these emails, most likely, are a "self-directed" "self-directed" carefully designed by Back to draw suspicion away from me by falsifying correspondence with Chinese。
So I decided to ask Back for metadata on these emails. The so-called metadata, like envelopes, postmarks and waxes of entity letters, can show the origin of the mail, the timing of its dispatch and whether it has been tampered with. Copies of those messages, which were made public during the Craig Wright London trial, did not contain that information。
I don't really expect metadata to provide critical clues. China is using an anonymous mailbox service registered in Tokyo, which itself hides the IP address; let alone, he is likely to further enhance anonymity by visiting these services through Tor. But I'd like to take a chance and maybe find something。
However, when I sent this request to Back, he did not respond. I was not sure whether he was deliberately avoiding it, or whether he was just busy with other things, and I didn't want to ask him immediately in order not to alarm him, so I waited eight days to send a second e-mail — and there was still no reply。
I obviously touched a sensitive point. But the question is: Why? What else could be deliberately concealed when China has taken such a tight protective measure? Unless he really left something wrong。
Nakamoto appears, Back disappears
After the publication of the Bitcoin in 2008 on Halloween, the system was improved over the next two and a half years with a group of early lovers. These people were later referred to as the "bitcoin core developers" who, through Bitcointalk and e-mails, worked frequently with Chung and contributed to their respective software engineering capabilities. Then, on April 26th, 2011, Chinese men "disappeared" as they were known。
And Adam Back's behavior, in a way, is the opposite。
For more than a decade now, as long as the topic of "electronic money" appeared in the Cypherpunks or Criptography mailing list, Back was almost always involved in discussions and often published long, detailed analyses. But when bitcoin — the closest thing to his vision in the early years — actually appeared, Back almost disappeared。
Many years later, in his December 2013 edition of Let's Talk Bitcoin, he gave a different version: He told the moderator that when Bitcoin was born, he was "technically very interested" and "involved" in discussions on the Crystal mailing list。
I went through the mailing list from the fall of 2008 to the winter of 2009 and tried to find any traces of Adam Back's involvement in the discussions, but nothing. In fact, it was not until June 2011 that he spoke openly about bitcoin for the first time — six weeks after the "disappearing" of Chinese。
This long-high-profile promoter of electronic cash, who has made ideas very similar to bitcoin, has little interest in the first years of its existence。
However, when he was finally truly involved, the timing coincided with a new event that was sufficient to alert China. On April 17, 2013, Argentine cipherist Sergio Demian Lerner published a blog that revealed the size of the bitcoin held by Chung. On the same day, Back joined Bitcointalk。
One week later, Lerner published a follow-up article, and Back wrote in the comment section, "If you think you're too close to the truth, maybe you should stop thinking about Nakamoto."
All of a sudden, you're all into it
It all came so suddenly. Adam Back was almost "full admission" overnight. Shortly after introducing himself on Bitcointalk, he began proposing complex system improvements; in less than two weeks, he publicly called for the restoration of the independent "middle-heart" phrase in Wikipedia (the page had previously been deleted and consolidated into the Bitcoin page); and within 18 months, he created Block Chain Company Blockstream, which works to develop tools to make the Bitcoin network more accessible, faster and more private。
It also opens a new phase: Back quickly accumulating influence as one of the core figures in the small Bitcoin community at the time. In order to form the Blockstream team, he "discovered" a group of top Bitcoin Core developers from companies like Google and Mozilla, giving himself great voice in the monetary ecology of this number。
At the same time, he quickly accumulated wealth: for more than a decade, Blockstream and its associated corporate financing totalled $1 billion and the company ' s valuation once reached $3.2 billion。
It all seems, almost exactly the same as an idea... If Chung decides to "go back to the stage" in his real capacity and regain control over the system he created, it is likely that this is the way he works。
In the autumn of 2014, Adam Back, along with his team, Blockstream, published a white paper on one of his key innovations, "Pegged Sidechains"。
This paper, led by Back, refers to digiCash. This company, created in the late 1980s by a password scientist David Chaum, introduced the early electronic money system. But unlike bitcoin, digiCash relies on its own central server. When a company went bankrupt in 1998, its monetary system collapsed。
The paper goes on to say, "Reliance on central servers has become the Achilles of digiCash." This is almost the same as the one that was described five years ago as the reason for his failure - "The biggest difference is that there are no central servers. This is the fatal weakness of Chaum
One year later, in 2015, the Bitcoin community was deeply divided around the issue of "block expansion". A group of developers, Gavin Andresen and Mike Hearn, advocated a substantial increase in the size of blocks to accommodate more transactions。
This proposal, however, gave rise to intense controversy. Larger blocks mean a significant increase in the running costs of nodes — greater hardware and faster network connectivity are needed. Once these costs are difficult for ordinary users, the number of nodes will decrease and the network may be concentrated in a few large data centres. Once these centres form a conspiracy, the security of the Bitcoin network will be fundamentally threatened。
Back is clear and tough about this. On Bitcoin-dev mailing list, he wrote successively against the outreach programme, and his tone grew stronger。
At the height of the debate, an accident happened。
The silent, many-year-old list of Sino-Samamoto's sudden re-emergence of the mailing list, whose statements are in line with Back's height. This was the first time he had "speaked" after more than four years of disappearance (in addition to the short response of the previous year, which was used to deny media exposure)。
At that time, a number of people in the Bitcoin community expressed doubts about the authenticity of the "middle-heart mail" — after all, his other mailbox account had been hacked. But Adam Back publicly endorsed it. In a series of tweets, he described the content of the e-mail as "very well judged" and said that it "consistent with China's long-standing views" and even quoted it several times。
Later on, Back was probably right: to date, there was no evidence that the mail had been forged, nor was more mail coming from the account。
More interestingly, the tone of the e-mail was highly similar to what Back had said in the previous few weeks of discussions, but little attention had been paid to it. As in Back, China stressed in the mail that the growing centralization of the Bitcoin network would threaten its security; he called the "very dangerous" "large block" -- a term that Back used repeatedly before。
In addition, there are a number of phrases in the mail that are commonly used to express a high degree of resonance with Back, such as "widespread consensus" "consensus rules" "technical" "difficult" "robust" etc。
At the end of the e-mail, he directly criticized Gavin Andresen and Mike Hearn as reckless developers who were trying to hijack Bitcoin by "populent means" and wrote, "It's very disappointing to see things go this far."
Four days later, in the same series of discussions, Back wrote an almost identical sentence: "Very disapproving, Gavin and Mike."
Close to the truth
Another possibility
I began deliberately to "reverse" my judgment. Late in the night, in bed, or in the morning bath, I repeat: Where can it go wrong
One of the points I saw in The Mysterious Mr. Nakamoto was convincing. In his book, Benjamin Wallace mentions that Adam Back is a "privileged absoluteist" while Bitcoin's design for privacy protection is relatively weak — neither seems to match。
This argument appears to be valid at first glance. But further, the situation is not simple. Unlike Cypherpunk, which had reservations about the coin due to lack of privacy, Back did not reject the system. Instead, over the past decade, he has continued to promote a series of technological innovations in Blockstream that seek to enhance the privacy of Bitcoin. This, on the contrary, weakens this argument。
Back himself gave another "self-cleaning" argument on X: When he first entered the Bitcoin community, he asked too many "low-level questions" on the IRC channel #bitcoin-wizards, which did not meet the technical standards of Chinese and Chinese。
#bitcoin-wizards IRC channel, which is essentially a technology discussion chat room where the Bitcoin core developer (also known as the "witch") will come together to discuss how to fix loopholes and improve software。
I looked at these conversations, but I hardly saw a "technology white" shadow. On the contrary, Adam Back has an impressive sensitivity to the potential hole in bitcoin. In the few weeks that he had been involved in the discussions, he had focused heavily on how to strengthen system security. Some of the improvements he had proposed were complex enough to go beyond the understanding of other developers。
I also note that his attitude towards other encrypted currencies is extremely cold, and he even stated his desire to “eliminate them all”。
What about the other "scientific candidates"? Does anyone fit this picture better than Back
In 2015, The New York Times presented a mainstream view: Szabo, a Hungarian American computer scientist, introduced a bitcoin-like concept in 1998. Szabo has long been at the top of the most popular guess list。
RECENTLY, HOWEVER, A HEATED DEBATE OVER THE UPGRADE OF BITCOIN CORE SOFTWARE ON X HAS REVEALED A CLEAR LACK OF UNDERSTANDING OF SOME OF THE BASIC TECHNICAL DETAILS OF BITCOIN, WHICH HAS SHAKEN HIS JUDGEMENT。
The other two who are often mentioned are Hal Finney and the software engineer, Len Sassaman, the privacy advocate。
With regard to Hal Finney ' s hypothesis, one obvious problem is that in April 2009, he was filmed as participating in a 10-mile long run, while almost at the same time, Chinese genius was sending mail and bitcoin to others. More importantly, during his last appearance in mid-August 2015, Finnney and Len Sassaman were both dead -- Finnney died of freezing in 2014 and Sassaman committed suicide in 2011。
As for the candidate for the HBO documentary, Peter Todd, the central evidence comes from a discussion on Bitcointalk in 2010 - Todd was able to "correct" a technical detail. According to this documentary, it may actually be that Sino-Hungmin “complements his point of view with another identity”。
But the problem with this inference is that it requires us to believe that a person who is extremely cautious about the anonymity of the network and the security of its operations will make the most fundamental mistake — to register to speak in his true identity. Moreover, Todd was only 23 years old at the time of the Bitcoin White Paper, and it would seem unreasonable in itself to deal independently with a problem that has beset many senior cipherists。
More realistic evidence comes from the time line - after the documentary was aired, Todd provided a photo to Wired showing the point of time at which he was active in China, where he was on a ski or cave expedition。
It has also been suggested that Bitcoin is not the product of one person but of a small team. But that is equally difficult to establish. The more participants, the more likely they are to leak. And the mystery of the middle-heart identity has remained close to water for the last 17 years。
Code is stronger than language
Of all the candidates, Adam Back is still the one I think is most likely. But at this stage, it's not enough just to look like the most. I started looking for more convincing "legal" evidence。
One day, when I looked through the Cypherpunks e-mail files, I suddenly noticed a detail -- that moment almost got me out of the chair。
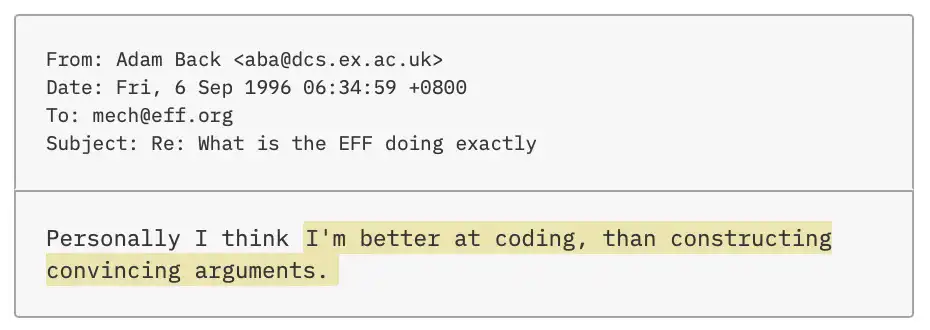
In this post, he explained to Hal Finney that, if it was clear to him that bitcoin would be easy to accept, he added, "I'm better at code than I am in expression. Better with code than with words
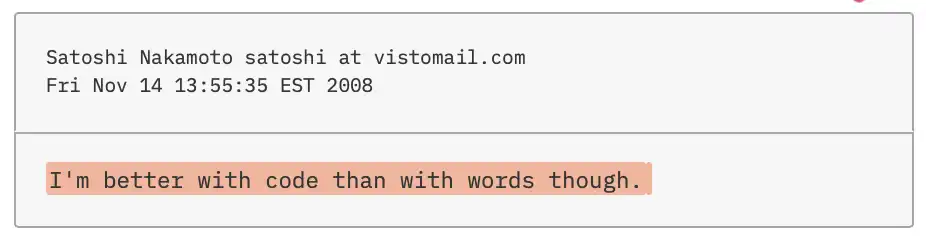
Adam Back, in a debate with another Cypherpunk on anonymity and freedom of expression, expressed similar views in similar language:
The more I look at it, the more I can discover the similarities in writing style。
As in Chinese, Adam Back uses two spaces between sentences -- This is an outdated writing habit, which usually means that the author is over 50 years of age. And Back this year 55 years old。
On Bitcointalk, he complained about the difficulty of explaining his invention to the general public, using the English-style exclamation word "bloody". And in October 2023, in a number of posts on X, Back insisted that he had never used the word: "You can search for it yourself, I never use it."
But I found a 1998 Cypherpunks mailing list in which Back expressed growing dissatisfaction with Internet banner ads with "bloody": "It's getting ridiculous now, and most of the bandwidth of my reliable 28.8k modem is occupied by these damn banner ads!"
If he has nothing to hide, why deny so resolutely that he has used the word
one of the most reliable ways to identify authors is by measuring the frequency and spacing of the use of functional terms such as "the" and "of" "to"。
In 2022, Florian Cafiero, a computational linguist from École nationale des arts of France, used this method to assist The New York Times in identifying two people behind the QAnon movement. But in providing an analysis of Benjamin Wallace's book, he tried to identify the wise but failed to reach a conclusion。
I thought he might have missed something and asked him to try again, and he agreed。

Adam Back was a photo of a meeting backstage in Miami in February this year. (Source: The New York Times, Photo: Amir Hamja)
When Florian Cafiero first analysed, Back was already one of the candidates. However, the analysis at that time was limited by the fact that most of Back ' s papers were co-authored with other cipherists, and it was difficult to judge what was in his hands。
On this occasion, Cafiero removed all his co-authorships and retained only the Back Hashcash and his doctoral dissertations and placed them in a sample pool of 12 academic papers from the "middle-hearing candidates", including Hal Finney, Nick Szabo, Len Sassaman and Peter Todd。
Because of the busy teaching and other projects, about six weeks later Cafiero gave me the results. During this period, I contact him through Signal almost every few days to ask if there are any new developments. Despite my efforts to control expectations, my inner expectations continue to rise。
The final result was sent by text message in late July: after comparing the 12 candidates ' papers with the Bitcoin White Paper, the Cafiero program showed that Back was the closest match。
At the same time, however, he stressed that the match was not "close" and that Hal Finney's results were very close and almost impossible to distinguish. The overall conclusion of this analysis therefore remains uncertain。
I can't believe I'm staring at the phone screen. It's like someone put a chocolate moose in front of me and took it away before I could taste it。
Discovering my frustration, Florian Cafiero changed the method of calculating the distance between the 12 candidates and the Chinese White Paper text. And it turned out to be the opposite of what I expected -- the other candidates outpaced Adam Back. According to Cafiero, this result is equally inconclusive。
After eight months of investigation and countless hours of retrospect with regard to the middle-hearing identity, I once thought I was close to the answer. But now the puzzle seems to be once again out of reach。
Spelling and Syntax:
Despite my disappointment, I actually generally know where the problem lies. Cafiero has reminded me many times that if he understands the principles of metrology, he can avoid recognition by deliberately adjusting his writing style。
I also noticed that Back, in a tweet from 2020, described his writing as "simplified and focused" and speculated that he deliberately reduced "emotional rhetoric, redundant adjectives, and run-off talk to reduce the risk of being identified by textual analysis." Apparently, both Chung and Adam Back have some knowledge of physical metrology。
In fact, Back started thinking early on about how to "counter" write analysis。
As early as the autumn of 1998, he wrote that the author of an alias could easily be identified if he wrote too much under his real identity. He even proposed the construction of a "multi-selection sentence generator" to select nouns, verbs and adjectives through a drop-down menu, thereby reducing the risk of personal writing habits being exposed。
On that basis, I turn to another approach — beginning with spelling and grammar。
Back interventions in the mailing list tend to contain a large number of spelling errors and loosely worded; and Chinese writing is simple, with little error. But after reading all the known texts of the deaf repeatedly and reading every article of the Back List, I caught some subtle, but consistent, writing habits。
Adam Back often confused "it" and "its" and used to put "also" at the end of the sentence. In the case of Chinese writing, these two situations occurred five times each。
They are also "problems" in the use of hyphen. Like Back, the Chinese are often added where no hyphenation should be added, but the addition is omitted. For example, he wrote the compound term "double-spinding" in the form of a hyphen, but the compound adjective like "hand tuned" "full blown" "woold be" "file shering" was not hyphenated – the same as Back。
In addition, when dealing with the composite adjective "noun + base " , they usually do not add hyphenation. In the mint base model, the mine was estimated of all transactions and deciped which contained first
they also display a clear "sway" in the spelling of some words. for example, “e-mail” and “email”, “built-in” and “built in”, “off-line” and “offline”, “pre-compiled” and “precompiled”, “to-do list” and “to do list” are used simultaneously; sometimes, “e-cash” is written and sometimes simplified to “e-cash”。
between british and american spellings, the two also switch: using both english and american "cheque" and the word "optimize" will change between british and american spellings. in addition, they sometimes write the word "backup" "bugfix" (although in verbs it will be removed) and the word "halfway" "downside" in the form of "half way" "downside"。
When I took these writing habits to Robert Leonard for analysis, he said that this was exactly the detail that they were following when they identified the author. He refers to these as "markers of sociolinguistic variation", a language fingerprint that helps to judge the author's social background, geographical origin or vocational training. The most valuable of these are the characteristics that appear only in the case of a few individuals, even individuals. He said that such characteristics were the most visible. And I have found at least three examples of what meets this criterion in the Chinese-heart text。
The first two are the special habits of Chinese in spelling encryption terms. One of them is "proof of work". The term was first proposed by two cipherists in a 1999 paper and was used to describe a solution protocol similar to Hashcash. According to the grammatical norm, they are used as complex terms and therefore are not hyphenated。
But the middle-hearing added. In the Bitcoin White Paper, he wrote "proof-of-work" several times. Before that, there were only eight hyphens in the Cypherpunks or in the password mailing list。
In an effort to narrow it down even further, I think that Chinese Chung mentioned in his email to Martti Malmi a colder Russian online currency, WebMoney. Only four of the people identified in the CyberMoney list or password mailing list have been identified。
I cross-referenced these four names with the eight people who use "proof-of-work" — there's only one overlap: Adam Back。
Another less visible expression is "partial pre-image". Before China used it to explain a bitcoin mining mechanism like Hashcash, I found only two people who used the term: Hal Finney and Back, and also discussed Hashcash. But there's a key difference between the two: Finnney writes "preimage", and Back prefers to add hyphens - in line with Chinese。
My third language tag is "burning the money." When he discussed the hosting mechanism (escrow), he used the term to mean "destruction of bitcoin". And before him, the only person who mentioned the notion of "burning" electronic money in the Cypherpunks or on the password mailing list was Back - April 1999。
From 34,000 to 1
I was hoping to find a more systematic way to analyze the writing style of Benn, and I got the help of the reporter Dylan Freedman of The New York Times' artificial intelligence team, who had extensive experience in computing text analysis。
One of my core judgments is that China is likely to belong to the community of coders active in the Cypherpunks, Criptography and Hashcash mailing lists — because he knows several Cypherpunk members, published white papers on the Criptography mailing list and integrated the Hashcash mechanism into the Bitcoin system。
So we collected all three mailing lists from the Internet and consolidated them into a large searchable database。
Between 1992 and October 30, 2008 (that is, the day before China's first appearance), more than 34,000 users posted on these lists. Because of the large number of users who have either a garbage account number or a small amount of content, we have first removed fewer than 10 postings and reduced the number of candidates to 1,615。
Then we further excluded users who had never discussed the digital currency and eventually reduced the pool to 620 candidates. This 620 total left 134,308 postings。
Ideally, we should have analysed these data without prejudice. Philosophy has always been proud of it, and Florian Cafiero has repeatedly emphasized it to me. But the reality is that this approach has not worked。
So we tried another path: finding the words "no synonyms" in the Chinese version and counting who used them most of the 620 candidates. Such terms are often technical terms that effectively exclude interference with common terminology. At the same time, this approach also circumvents the "multi-selection sentence generator" that Adam Back had previously conceived, because words without synonyms are difficult to replace。
We tested it. The results show that Back is in the first place — he shares 521 “no synonyms” with Chinese. Although there are other Cypherpunk members close to this level, their number of postings is much higher than that of Back, which in turn makes his results more prominent。
To find more decisive evidence, we have designed two new approaches based on previous investigations。
first of all, we focus on the syntax error in the use of the hyphen。
In the analysis, we use The New York Times style manual as the "correct standard" and input its rules on hyphenation into an AI model. The model is then scanned to the full text of this brain and eventually identifies 325 different hyphenation errors。
When we compared these errors to the writings of hundreds of candidates, Back's results were extraordinary. He had 67 completely the same mistakes as Chung, and only 38 were ranked second。
Back to the original 620 candidates, I would like to confirm further: how many have other writing habits that I have identified in the Chinese text
As a first step, we screen those who occasionally use two spaces between sentences, like Chinese. This condition directly excludes 58 persons and narrows the candidate list to 562 persons。
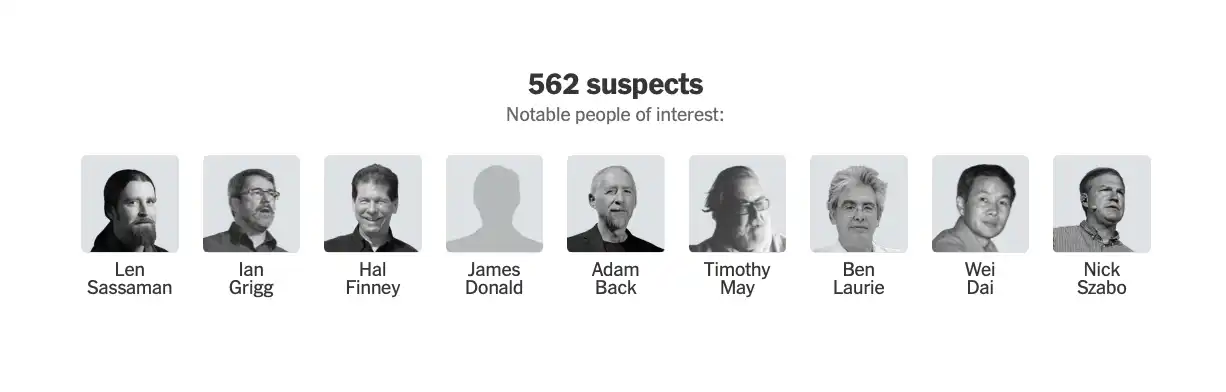
Of these, nine are well known as "sweet-hearing candidates"。
next, we screen out those who use english spelling to narrow the list down to 434 people. then we looked at those who sometimes confused "it" with "its" and "its," a step that further narrowed the range of candidates to 114. the number of those who occasionally use "also" at the end of the sentence dropped to 56。
among the 56, we have removed those who wrote "bug six" into two words, while at the same time writing "halfway" and "downside" into one word, and reduced the number of candidates to 20. while the number is still modest, it is much easier to handle than it was initially。
next, we exclude those who correctly use hyphens in the composite adjectives "noun-based" and "file-sharing" but do not use hyphens in the composite noun "double sprinting" (which is the opposite of the chinese-heart habits). as a result, the number of candidates was reduced to 8。
finally, we ask the database: how many of the eight remaining people, like chung, switched between "e-mail" and "email", "e-cash" and "electronic cash", "cheque" and "check" and "optimize" american spellings
There's only one answer: Adam Back。

Adam Back created a new Bitcoin Treasury. (Source: The New York Times, Photo: Amir Hamja)
Face-to-face
El Salvador
I still do not have decisive evidence that will lead to the final confirmation of my middle-heart identity. In theory, such certification can only be completed by the Chinese himself, using a private key linked to one of the earliest blocks of Bitcoin. But at this point, I've accumulated a lot of clues。
In mid-November, I wrote to Back again to apply for a new interview. This time, I didn't bend again. I was straight in the mail, and I've come to the conclusion that... He is Chinese and wishes to show him all the evidence I have and give him an opportunity to respond. I even offered to fly to Malta to communicate in person。
He has still not replied。
So I decided to change it. In two months, he will attend and deliver a Bitcoin conference in El Salvador, where I intend to approach him in person。
I arrived in late January in San Salvador, where the climate is warm, and I have plans. The round table of Adam Back was scheduled for the second day of the General Assembly, when I had planned to approach him again. But later in the afternoon of the first day, I noticed that he had posted on X a photograph of himself speaking at the floor. When I was confused and worried about missing the opportunity, I ran to the guest room of the speech, thinking that maybe I could find him there. But the security officers refused to let me in, so I kept an eye on the entrance。
About 30 minutes later, Back went out. I'll come up and introduce myself. He was somewhat confused, but, to my surprise, he agreed to meet him in the lobby of the hotel where he was staying the next morning, which was also the venue of the conference。
At the appointed time, I found out that Back was still with two of his top executives at a new Bitcoin Treasury. He explained that the company was in the process of being listed, which made it necessary to be more cautious in his contacts with the media。
I had not noticed this at all before. The so-called Bitcoin Treasury is a large-scale holding of bitcoin by borrowing funds, thus providing investors with a more radical way of betting. Back was created last summer, and it is being merged with a listed shell company set up by Cantor Fitzgerald, a Wall Street company led by United States Secretary of Commerce Howard Lutnick. As chief executive officer of the consolidated company, Back needs to comply with United States securities law and disclose all information that has a " significant impact " on investors. For example, if there is a secret hold of up to 1.1 million bitcoins, such information may well fall within the scope of disclosure once the sale may impact the market。
While digesting this new situation, we went up to the hotel room in Back with four people. Back in black T-shirts and black long pants, with a slight tan, the whole person seems to be relaxed。
In the next two hours, I'll have the evidence in front of Adam Back. And he denied himself repeatedly, with a soft and English accent, that he was a middle man, and reduced all this to a series of coincidences. At some point, however, his body language revealed different messages. When faced with more difficult questions, his face was slightly red, and he seemed a little restless in his seat。
For example, Back did not give a convincing explanation why he "disappeared" from a coded mailing list during China's smart and active period, but merely stated that he was busy. Similarly, he cannot explain why he claimed to have been involved in the mailing list discussion around the Bitcoin White Paper at the end of 2008 in a podcast called Let's Talk Bitcoin - a fact that shows that he was not involved. As I continue to pursue these two issues, his attitude has clearly become more defensive。
"In the end, it doesn't prove anything. I can assure you, it wasn't me." He said that with sharper tone。
When I mentioned the results of our analysis of writing styles, Back was full of words, trying to find an explanation that failed. "I don't know," he said, "It's not me. But I understand what you're saying -- these are based on data and AI. But it's still not me
Adam Back argued that it was difficult to prove a “do not exist”. But he still offers one thing to prove innocence: When he first joined the #bitcoin-wizards IRC channel, bitcoin was poorly understood, and at one point it was mistakenly assumed that bitcoin addresses were similar to bank accounts that would vary with the balance. (In practice, the Bitcoin address is more like a wallet with cash, and the transaction is made in a completely new digital currency
The problem is that this "misunderstanding" does not leave any traces in the chat records. And when I pointed out that, Back responded with a slight response: "If this is my own fantasy, it would be so funny. He later added in his email that this could also happen on another unrecorded IRC channel
Back denied that he was a middleman more than six times. But I was impressed by one of the denials — when I pointed out that he had conceived almost all the core elements long before Bitcoin was born, he said, “It is clear that I am not the middle-minded, this is my position.” This is more like a “statement of position” than a factual assertion. But soon he added, "And it is true."
On some issues, Back agreed with me. He recognizes that he has the background and technical skills to become a middle-minded; he also recognizes that he is likely to be British, over 50 years of age, and belongs to the Cyprus community. At the same time, he agrees with me that there is a contradiction in his correspondence with Chinese mail: If Chinese had read his Hashcash paper, it would have been impossible to be unaware of the b-money that Wei Dai had proposed。
However, he denies that the e-mails are carefully designed to divert the outside world from their own suspicions. If he is willing to provide metadata for these messages, this denial may be more convincing — but he has never responded to my request for metadata。
I had a few more questions to ask Adam Back, but his assistant said he had other meeting arrangements. Together, we went back to the lobby in the elevator and shook hands like two chess players who had just ended a fierce match。
When I watched him disappear among a group of relaxed participants, there was a lingering doubt in my heart. For a moment, I felt like he was missing something — as if he was speaking as a middleman. But at that time I couldn't think of the exact words。
Back in New York, I found that moment in the interview. That is when I combed with him the similarities between what he said and what he said. I mentioned the words of the middle man, and before I could explain why, Back interrupted me。
A few days later, I e-mailed him to testify. He denies that this is a "speech." He said, "I'm just responding to a general phenomenon through dialogue. – Many technicians are more comfortable expressing their ideas in code than in words.”
But at that time, I made it very clear that I was asking for a specific medium-heart, and I doubt that Back actually realized that。
I can't help but think of the fact that a decade ago, Sino-Bun-yung "re-emerged" helped Back win a key battle in a block-up struggle. At this moment, it seems that again, in this luxury hotel in El Salvador, China seems to have appeared. Only this time, he helped Back in the opposite way — to dispel my last doubt and convince me that I found the right person。
I said, "I'm better at writing codes than speaking in words."
Back said, "But I said a lot. I mean, I'm not saying I'm good at expression, but I do write a lot on these mailing lists."
As I hear it, the subtext of this sentence is: for a man who is better at code than language, he writes a lot. And this in itself, as if it were an admission — that's what he wrote。
In other words, just in a few seconds, Back seems to have put down his disguise and turned back into Chinese。
[ Chuckles ]Original Link]