The Age of the Networking of Things: The Land Sweeping Robots will steal your encrypted currency

Original title:My robot vac is showing my Bitcoin:
Original by Felix Ng, Cointelegraph
Original language: Deep tide TechFlow
Smart sweep robots and other smart home devices can easily be hacked to record your password input or assistive words。
Imagine, one morning, when I woke up and the machine was out of control, the fridge started demanding ransoms from you, and your encrypted currency and bank account funds were looted。
This is not the story of Stephen King's horror film "Maxum Overdrive" of 1986, which tells the story of a homeless comet that triggered a worldwide wave of machine killings。
On the contrary, if hackers break into your computer through your home's smart device, they can pose a real risk. As the number of IOTs is projected to reach 18.8 billion worldwide, the probability of this scenario is increasing with an average of about 820,000 Iot attacks per day。
“Insecure items of networked equipment (such as routers) may be an entry point for intrusion into family networks”, Tao Pan, a researcher of the block chain security company Beosin, stated in an interview。
As of 2023, ordinary households in the United States had an average of 21 connected devices, one third of whom had experienced data leakage or fraud within the last 12 months。
“IN THE EVENT OF HACKING, THE ATTACKERS CAN MOVE HORIZONTALLY TO ACCESS CONNECTED EQUIPMENT, INCLUDING COMPUTERS OR MOBILE PHONES USED FOR ENCRYPTED CURRENCY TRANSACTIONS, AND CAN ALSO CAPTURE LOG-INS BETWEEN THE EQUIPMENT AND THE EXCHANGE. THIS IS PARTICULARLY DANGEROUS FOR USERS WHO TRADE IN ENCRYPTED MONEY USING API," HE ADDED。
So, how does a hacker steal itWhat's your family's informationWhat harm can it cause
Magazine collected some of the most surprising hacking incidents in the past few years, including a case where a prohibited sensor had been hacked to dig up encrypted currency. We have also collated a number of practical recommendations to protect data and secure encrypted money。
Intruding on the coffee machine
In 2019, Martin Hron, a researcher at Cybersecurity Inc., demonstrated how hackers can easily access family networks and their equipment。
He chose a simple target: a remote intrusion into his coffee machine。
Hron explained that, like most smart devices, coffee machines use default settings to connect devices to WiFi without passwords, making it easier to upload malicious codes into machines。
“Many items are first connected to a family network through its own WiFi network, which is used only to install equipment. Ideally, consumers would immediately use the password to protect the WiFi network, “Hron explains。
“But many of the equipment left without a password to protect the WiFi network, and many consumers did not have a password,” he added。

Original video link: click here
"I can do whatever I want, because I can replace the solid, the software for the coffee machine. And I can replace it with anything I want. I can add functionality, delete functionality, and break down built-in security measures. So I can do whatever I want," he said in the video released by Avast。
In his presentation, Hron showed a blackmail letter through the coffee machine, and the equipment was locked out of use unless a ransom was paid。
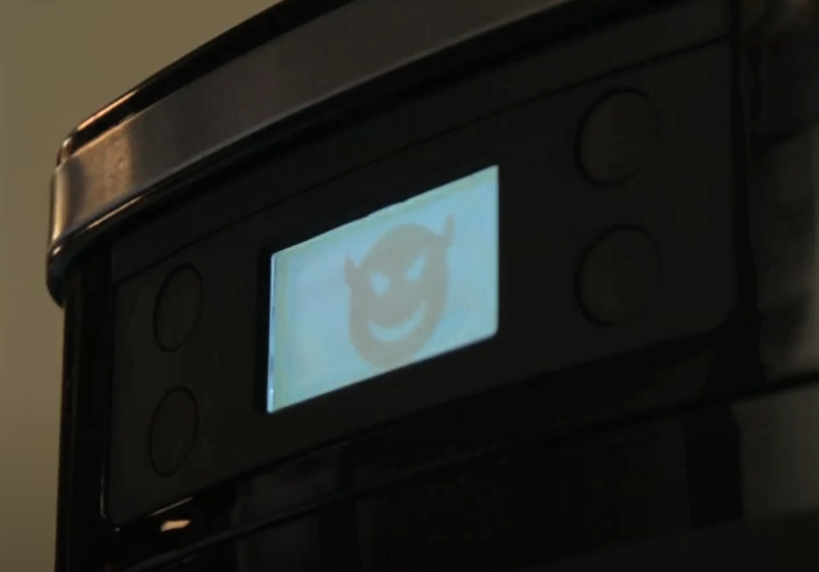
You can switch off the device, but that means you can't drink coffee anymore
(Avast/YouTube)
However, in addition to displaying letters of extortion, coffee machines may be used to carry out more malicious operations, such as opening heaters to create fire hazards or spraying boiling water to threaten victims。
Worse still, it could be a quiet entry into the entire network, allowing hackers to monitor your bank account information, mail and even encrypted notes。
Intruding the casino fish tank
ONE OF THE MOST FAMOUS CASES OCCURRED IN 2017, WHEN HACKERS TRANSMITTED 10GB DATA THROUGH A FAMOUS CASE OF HACKING INTO A NETWORKED FISH TANK IN A CASINO HALL IN LAS VEGAS。
Fish tanks are equipped with sensors for temperature regulation, feeding and cleaning, which are connected to a computer on the casino network. Hackers enter other regions of the network via fish tanks and send data to remote servers in Finland。

The fish tank may look like this
Muhammad Ayan ButtUnsplashI'm not sure
Despite the deployment of conventional firewalls and poison-killing software in casinos, the attacks were successful. Fortunately, the attacks were quickly identified and dealt with。
Cybersecurity, DarktraceBBC: “WE STOPPED IT IMMEDIATELY, WITHOUT CAUSING ANY DAMAGE.” SHE ADDED THAT THE GROWING NUMBER OF INTERNET CONNECTIONS MEANT “THE PARADISE OF HACKERS”。
Door sensors can also steal mine
In 2020, in offices that were shut down as a result of the new coronation, Cybersecurity, DarktradeGot itIn a clandestine, encrypted currency mining incident, hackers used the control office's biologically closed servers to carry out illegal mining。
The clue to this incident stems from the fact that the server downloaded suspicious enforceable documents from an external IP address that had not appeared on the network. The server then connects several times to an external end point related to the private Monero mine。
This attack is called"Cryptojaking"In 2023, the Microsoft Threat Intelligence team discovered more such attacks, and hackers targeted Linux and connected to the InternetSmart device。
The Microsoft survey found that the attackers would launch attacks by violent hacking of Linux and Internet-connected devices. Once they enter the network, they install backdoor programs and then download and run the encrypted currency mining malware. This would not only lead to a sharp increase in electricity costs, but would also result in the direct transfer of all mining proceeds to hacker's wallet。
ONE OF THE MOST RECENT CASES, INVOLVING THE EMBEDDING OF ENCRYPTED HIJACKING CODES ON A FAKE PAGE OF 404 HTML, IS THE PROLIFERATION OF SUCH HIJACKINGS。
Hacker intrusion smart device:Destroy the grid
Worse still, the security researchers at Princeton University have made the assumption that if hackers can control enough high-energy equipment, such as 210,000 air-conditioning units, and turn them on at the same time, this could lead to a sudden power outage of about 38 million people in California。

(Unsplash)
Such equipment would need to be concentrated in a certain part of the grid and opened at the same time to cause current overloading of certain power lines, thereby damaging or triggering protected relays on the lines to shut down. This will transfer loads to the remaining lines, further exacerbate the grid pressure and eventually trigger a chain reaction。
However, this situation requires precise malicious scheduling, as grid fluctuations are common during special weather periods, such as heat waves。
The sweeper is watching you
Last year, the U.S. Land sweep robots suddenly started on their own. Turns out the hackers discovered a serious security breach in a Chinese-made Ecovac machine。
It is reported that hackers can remotely manipulate these devices, use them to intimidate pets, shout dirty language to users through built-in loudspeakers, and even use built-in cameras to spy on the user ' s home environment。

A picture of a blacked Ecovac sweep robot in real time
I'm sorryABC PUBLIC INFORMATIONI'm not sure
“A serious problem with Internet-connected equipment is that many manufacturers are still not paying enough attention to security issues”, indicated by the network security company Kaspersky。
Clearly, if hackers had access to video images of you entering passwords or recording assistive words, the consequences would be difficult to imagine。
How can you protect yourself from smart device hacking
Looking around, you may find that almost all the devices in your home are connected to the Internet -- ground sweep robots, digital frames, doorbell cameras. So what are you gonna doKeep your bitcoin safeAnd
One option is to use professional hacker Joe Grand: completely avoid using any smart device。
“My phone is the smartest device in the family, but even so, I'm reluctant to use it for navigation and communication with my family”, he told Magazine, “But smart equipment? Absolutely impossible.”
Avast's Hron indicates that the best way is to ensure that passwords are set for smart devices and avoid default settings。
Other experts recommended the use of an independent visitors ' network for physical networking devices, especially those that did not need to share the network with computers and mobile phones; disconnecting equipment when it was not in use; and keeping the software up to date。
In addition, there is a network feeSearchEngines to help users look at home connected devices and possible loopholes。
RECOMMENDED READING:
RootData 2025 Web3 Industry Annual Report
The change of power in the currency: the dilemma of a 300 million-dollar empire
InfoFi narrative collapse, Kaito, Cookie, etc. stop the respective products