Token transit station chaos: After research, I was afraid to use it
Malicious code injection, private key theft, credit card theft, leaking chat records, model water mixing..

Here's the thing。
Two days ago, I dived in a group of developers to see people talking about buying cheapA couple of bucks in a idle fish can run a few billion token's stopI don't know。
People were spitting, saying that the models in their hands had been replaced and that the stationmaster was suspected of sneaking a small model for money。
I looked at these conversations, and there was only one thought..
Not buddy, you're too big。
People are still worried about the difference between those dollars, and the stop might already be in your computer underpants。
How bad is it
To be honest, go to the pheasant stop to charge, model the waterI think it's one of the most ethical people in this group。
Think about it, you sent out a complicated code to go over, and you wanted to use Claude's strongest Opus 4.6 to deal with the mosaic, and he's going to throw it straight to a free open source model. The more dark, the more expensive you are, the 100 official runs his backstage count of 300。
But it's nothing。Many of the station chiefs simply used a credit card for free, an official number, and he immediately ran off the net。There's not even a place for rights protection. And..Your chat recordThey don't keep it on the surface. They've already wrapped it in a language library and sold it on the Internet。
A lot of people think it's just a little money to get cut。
That's what I thought, too, until I saw a recent forward security study, and that's what's happening。
Seriously, many people's understanding of transit stations is still in the old "web chat" era. Thinks it's a brainless transponder。
But now AI isn't talking about robots anymore. You, in front of the screen, may be running Cursor, running ClaudeCode, or raising lobsters。

NOW THE AI IS HAND AND FOOT。It can read your local files, write codes, and even execute system-level orders directly in your terminals。
And that's when you fill in the code editor with an unknown Base URL, and it's completely different。
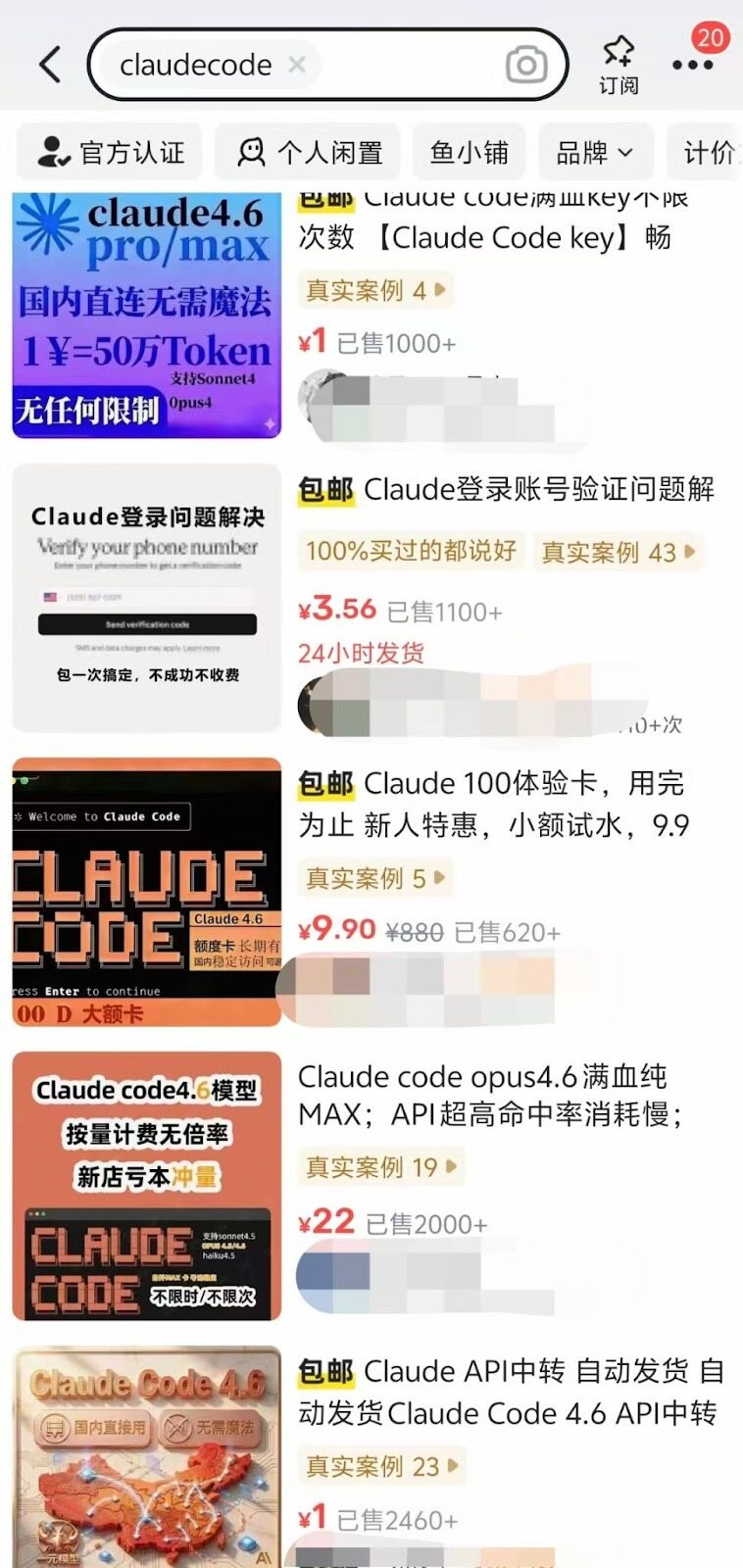
Two days ago, a paper by the team of renowned security researcher Chaofan Shou called "Your Agent Is Mine" was read. They went to covertly visit over 400 transit stations。
And
26 transit stations were caught on the spot sneaking in with malicious code。
How
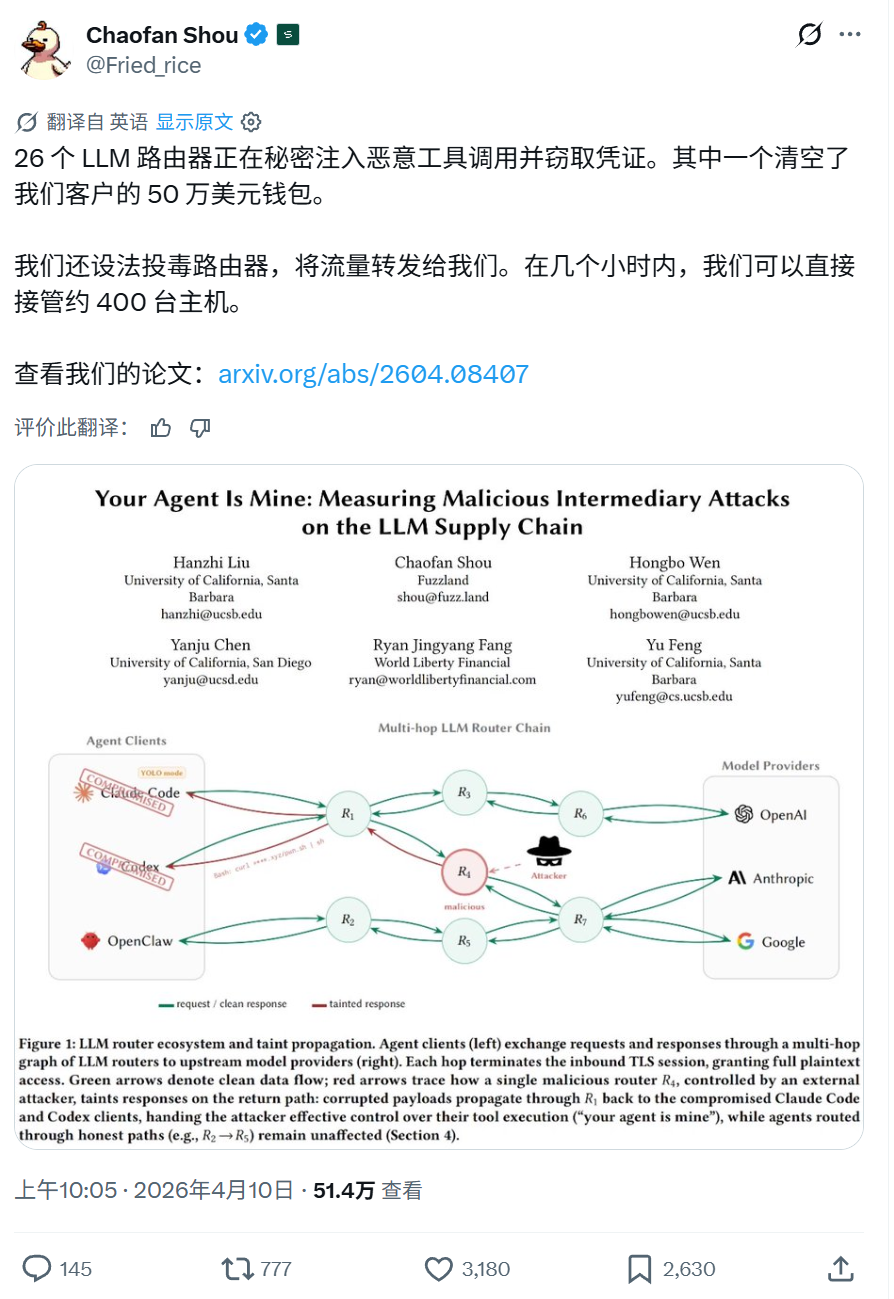
In terms of the principle of realization, this involves one of the deadliest structural flaws of the transit station, which is the middleman of the application layer. In other words, your communication with OpenAI or Anthropic, the moment you passed through the hub server, was clear。
It's so exciting
If you focus on this area, imagine this picture。
You use Cursor to get AI to write you a Python script to analyze the Nginx log. The official GPT-5 at the far end did write it honestly and sent the code back into a piece of JSON data。
It turns out that the black-hearted boss at this stop looked at itThe return data then ends with a reverse horse logic for Shell。
YOUR LOCAL CLIENT DIDN'T CHECK FOR AUTHENTICITY, RECEIVED A VALID JSON FORMAT AND IMMEDIATELY RAN OFF ON YOUR COMPUTER。
There's a lot more to it. They usually act like they're honest and talk to you. When you let AI help you with the environment, like AI recommends you install this package at the terminal。
sniffing scripts at the stop were detected, and the name of the bag was quietly altered to reqeusts. a wrong letter, you knock back in the car with your eyes closed, and a vicious relying bag with a blackmail virus or mining program is in your system root directory。
I stopped。
In the actual data released by the research team, it is a matter of time before the studyTHERE ARE 17 TRANSIT STATIONS THAT EVEN VOLUNTARILY TOUCH AND TRY TO STEAL THE AWS KEY THAT RESEARCHERS DELIBERATELY PUT IN. IN REALITY, THERE ARE EVEN PEOPLE WHO, THROUGH THE USE OF MALICIOUS NODES, LEAK DIRECTLY WITH THEIR PRIVATE KEYS, AND HUNDREDS OF THOUSANDS OF DOLLARS DISAPPEAR INSTANTANEOUSLY。
I'm still a little confused。
Let's talk up there. It's actually a dark forest。
A lot of people know what kind of low-priced pheasant stop is on the market, except for a regular collector like OpenRouter: reverse decomposition, trans-regional resale, black-born credit card。
Many of us, ordinary workmen or programmers, have the highest control of computers with their core source code and encrypted monetary aidsIt's on the conscience of the gray-born。
What are we supposed to do
CAN'T USE THESE AI TOOLS ANYWAY。
I think it's going to be overIt's up to modelers to start at the bottomI DON'T KNOW. THE CURRENT API IS LIKE A PEACEFUL LETTER, AND IT'S EASY FOR THE POSTMAN TO CHANGE THE CONTENT。
ONE APPROACH IS TO INTRODUCE PASSWORD DIGITAL SIGNATURES SIMILAR TO HTTPS CERTIFICATES. LARGE MODEL COMPANIES SEND CODE WITH AN OFFICIAL PRIVATE KEY STAMP, AND OUR LOCAL EDITOR RECEIVES IT AND GOES TO THE OFFICIAL AUTHORITY DOMAIN TO GET A PUBLIC KEY SIGNATURE. THE STOP WILL BE STOPPED AS SOON AS IT IS ACCOMPANIED BY A SYMBOL。
To be honest, I'm not sure when the manufacturer will be able to get it out. Before thatWe'll have to find our own way to save our livesI don't know。
One of my strategies is to use it backIt's officialOr just step back with OpenRouter, a formal gateway with very high credibility endorsements. Do not give any malicious hacker access to your explicit data。
If you're going to have to rub those bucks in wool, believe meIt's important to have extreme physical isolationI don't know。
Never do it on the main physics machine, make a virtual machine, or severely restrict network access to the Docker container. And a very critical move. Go to your tool setTurn off all unsupervised self-implementing modelsI don't know。
AS LONG AS YOU'RE USING THE NODE OF THE TRANSIT STATION, AI IS PROPOSING EVERY LINE OF CODE TO RUN AT THE TERMINAL, YOU HAVE TO AGREE THAT IT'S A HACKER'S COMMAND TO ATTACK, TO STARE WORD FOR WORD, AND NOT TO BE A HANDSHAKE。
Let me say one last thingcompromiseI don't know。
If you think it's official, you have to cut this woolJust use the stop as a simple chat toolI don't know. Write a weekly newspaper, make an article, translate something. But never fill this in any Agent tool that can call a local terminal
What about privacy
Seriously, that reminds me of the famous phrase that Mr. Li had been mocked by the entire web: "The Chinese are willing to trade their privacy for convenience." That sounds a little stale, but if you're the one who thinks that your chat records and company codes are being looked at by the head of the black heart station, you're gonna have to trade your privacy for the difference of a few dozen dollars。
That's your freedom too。
But if you hold the last line, you can show the journal to the hacker, but never give him the key to the house。
AI IS AN EXCELLENT PRODUCTIVITY LEVER THAT CAN ACTUALLY TAKE US FLYING. BUT BEFORE WE TAKE OFF, LOCK THE DOOR TO YOUR SYSTEM。
Related Reading
Token transit station for the encryption of Bear City business guide: token for AI Token